PermalinkSet Up External Portal Application Authentication with Okta and OIDC
These instructions help you set up Okta as your third-party identity provider for use with the Kong OIDC and Portal Application Registration plugins.
PermalinkDefine an authorization server and create a custom claim in Okta
Follow these steps to set up an authorization server in Okta for all authorization types.
- Sign in to the Developer Okta site.
-
Click Security > API > Authorization Servers.
Notice that you already have an authorization server set up named
default. This example uses the default auth server. You can also create as many custom authorization servers as necessary to fulfill your requirements. For more information, refer to the Okta developer documentation. -
Click default to view the details for the default auth server. Take note of the
IssuerURL, which you will use to associate Kong with your authorization server. -
Click the Claims tab.
- Click Add Claim. Add a custom claim called
application_idthat will attach any successfully authenticated application’sidto the access token.- Enter
application_idin the Name field. - Ensure the
Include in token typeselection is Access Token. - Enter
app.clientIdin the Value field. - Click Create.
Now that you have created a custom claim, you can associate the
client_idwith a Service via the Application Registration plugin. Start by creating a Service in Kong Manager. - Enter
-
Create a Service and a Route and instantiate an OIDC plugin on that Service. You can allow most options to use their defaults.
-
In the
Config.Issuerfield, enter the Issuer URL of the Authorization server from your identity provider.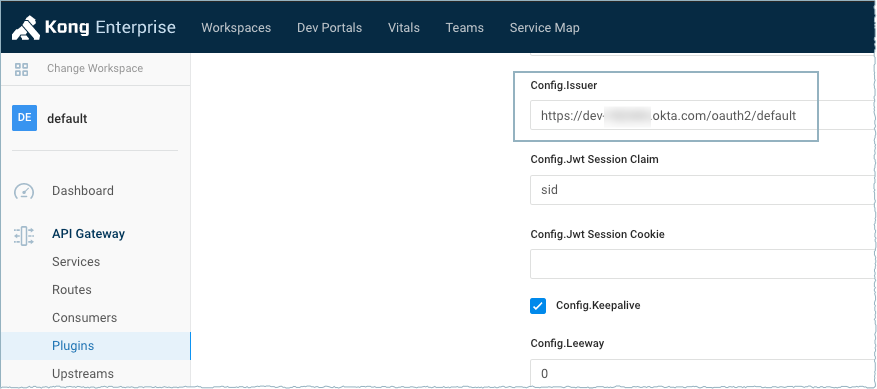
-
In the
Config.Consumer Claimfield, enter the name of the field from the Okta payload that contains the application ID. This is usuallysub.
Tip: Because Okta’s discovery document does not include all supported auth types by default, ensure the
config.verify_parametersoption is disabled.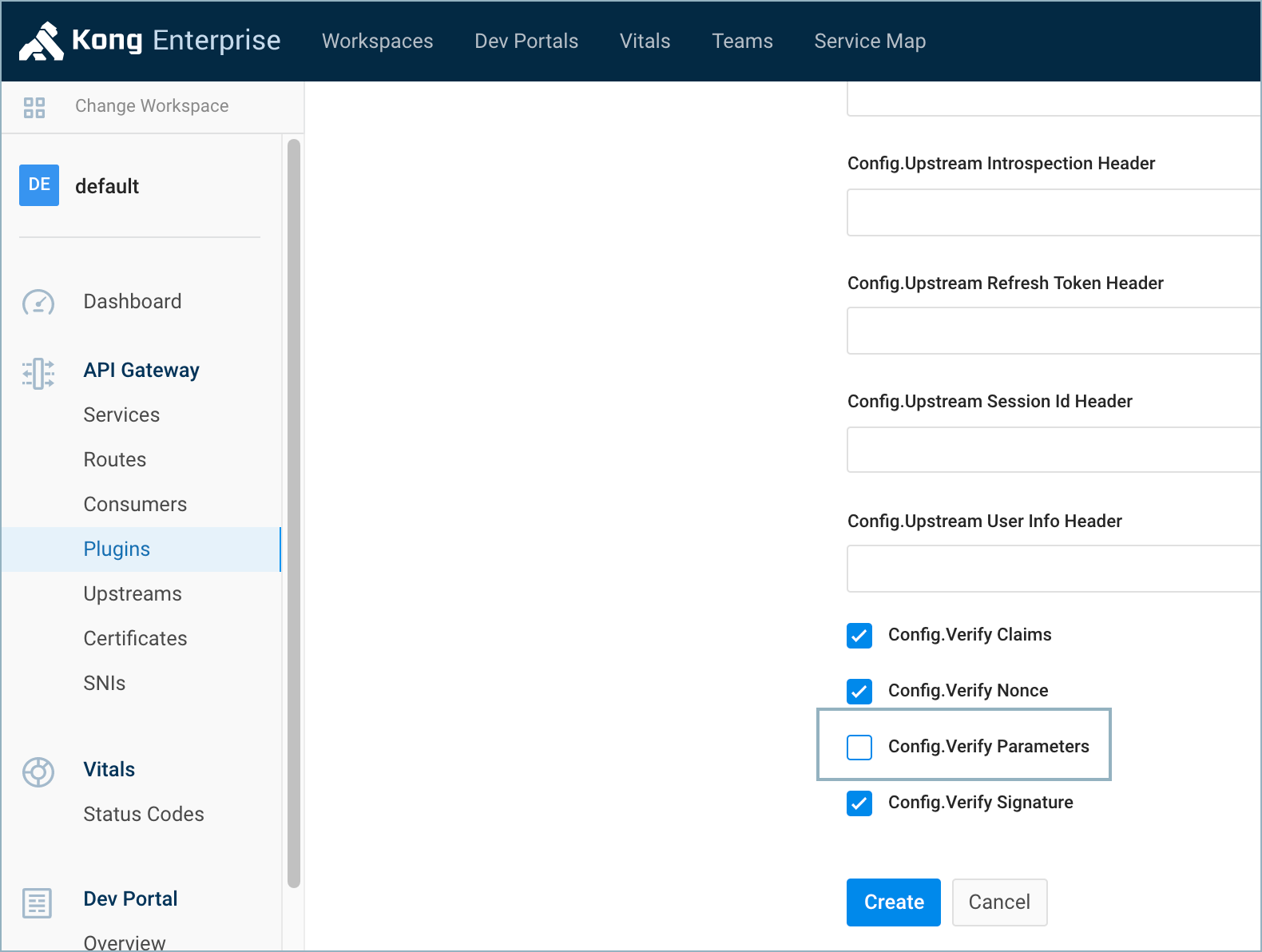
The core configuration should be:
{ "issuer": "<auth_server_issuer_url>", "verify_credentials": false, "consumer_claim": "sub", } -
- Configure a Portal Application Registration plugin on the Service as well. See Application Registration.
PermalinkRegister an application in Okta
Follow these steps to register an application in Okta and associate the Okta application with an application in the Kong Dev Portal.
- Sign in to the Developer Okta site.
- Click Applications > Applications.
-
Depending on which authentication flow you want to implement, the setup of your Okta application will vary:
- Create a new app integration: Select
API Serviceswhen prompted for an application type. In the New API Services App Integration modal, enter your app integration name.
You will need your
client_idandclient_secretlater on when you authenticate with the proxy.-
Implicit Grant: Select
Single-Page App,Native, orWebwhen prompted for an application type. Make sureImplicitis selected forAllowed grant types. Enter theLogin redirect URIs,Logout redirect URIs, andInitiate login URIfields with the correct values, depending on your application’s routing. The Implicit Grant flow is not recommended if the Authorization Code flow is possible. -
Authorization Code: Select
Single-Page App,Native, orWebwhen prompted for an application type. Make sureAuthorization Codeis selected forAllowed grant types. Enter theLogin redirect URIs,Logout redirect URIs, andInitiate login URIfields with the correct values, depending on your application’s routing.
- Create a new app integration: Select
PermalinkAssociate the identity provider application with your Kong application
Now that the application has been configured in Okta, you need to associate the Okta application with the corresponding application in Kong’s Dev Portal.
Note: Each developer should have their own application in both Okta and Kong.
Each Okta application has its ownclient_idthat maps to its respective application in Kong. Essentially, this maps identity provider applications to portal applications.
This example assumes Client Credentials is the chosen OAuth flow.
- In the Kong Dev Portal, create an account if you haven’t already.
- After you’ve logged in, click
My Apps. - On the Applications page, click
+ New Application. -
Complete the Name and Description fields. Paste the
client_idof your corresponding Okta (or other identity provider) application into the Reference Id field.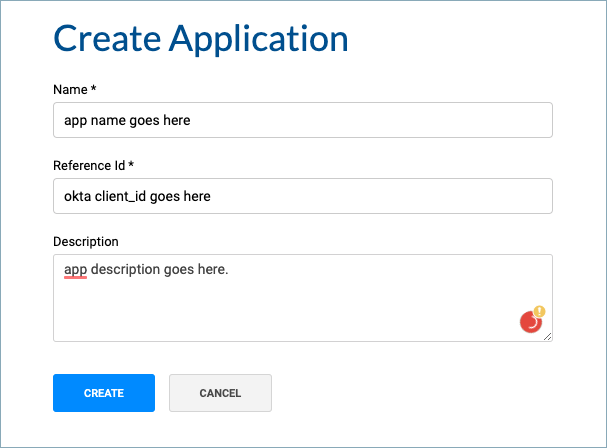
Now that the application has been created, developers can authenticate with the endpoint using the supported and recommended third-party OAuth flows.

