You can use Kong consumers for authorization and dynamically map claim values to Kong consumers. This means that we restrict the access to only those that do have a matching Kong consumer. Kong consumers can have ACL groups attached to them and be further authorized with the Kong ACL plugin.
Prerequisites
In most cases, the OpenID Connect plugin relies on a third party identity provider (IdP). The examples in this guide use Keycloak as a sample IdP.
Expand the following sections to configure Keycloak and Kong Gateway.
Configure Keycloak
All the *.test domains in the following examples point to the localhost (127.0.0.1 and/or ::1).
We use Keycloak as the identity provider in the following examples, but the steps will be similar in other standard identity providers. If you encounter difficulties during this phase, refer to the Keycloak documentation.
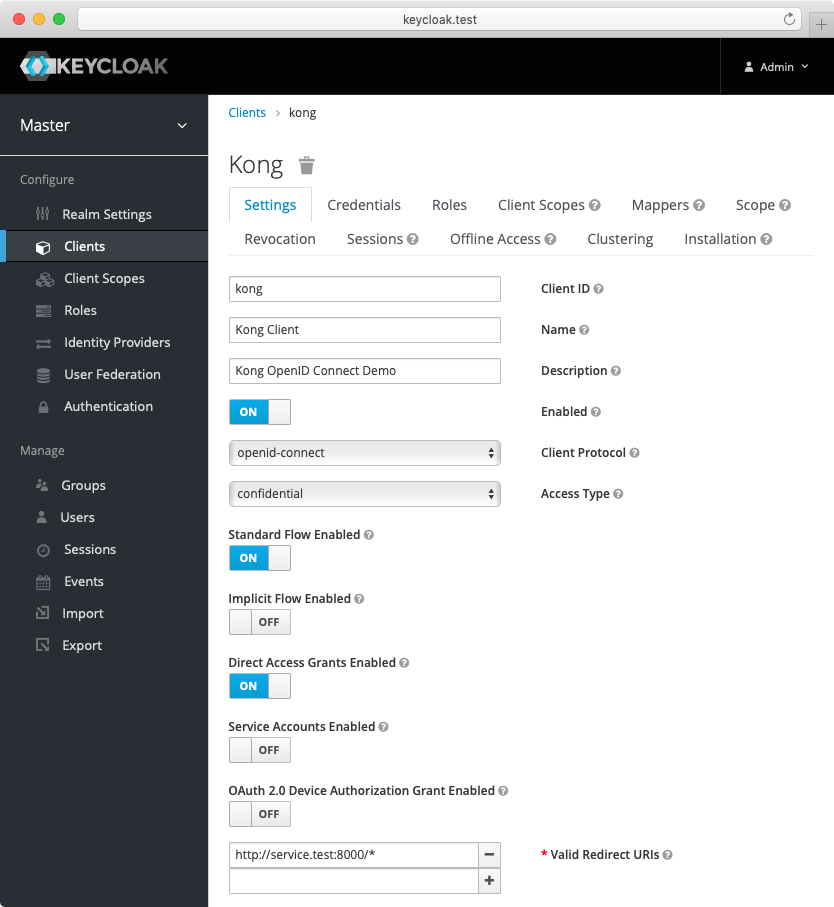
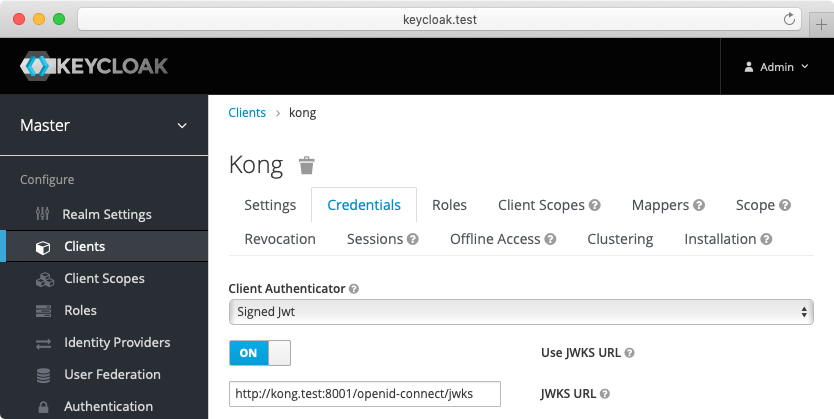
- Create a confidential client
kongwithprivate_key_jwtauthentication and configure Keycloak to download the public keys from [the OpenID Connect Plugin JWKS endpoint][json-web-key-set]:
-
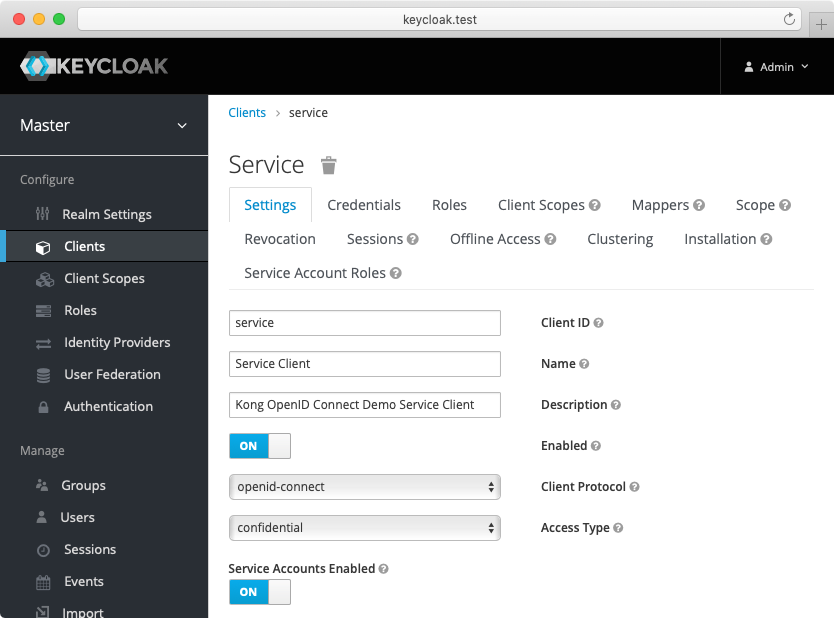
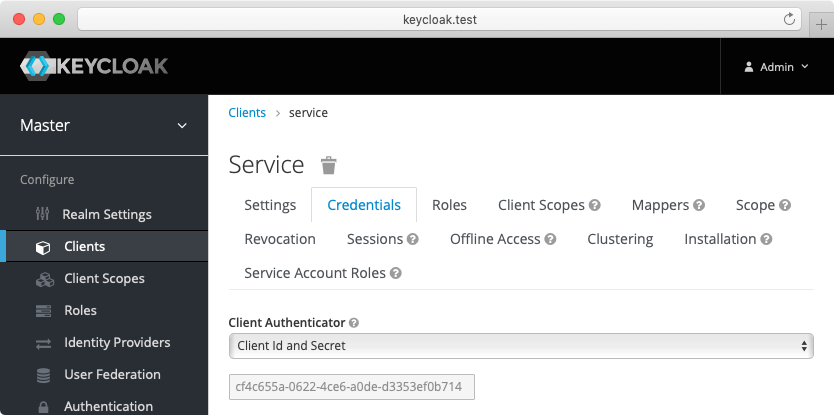
Create another confidential client
servicewithclient_secret_basicauthentication. For this client, Keycloak will auto-generate a secret similar to the following:cf4c655a-0622-4ce6-a0de-d3353ef0b714. Enable the client credentials grant for the client:
-
(Optional) Create another confidential client
cert-boundwith settings similar to theserviceclient created previously. From the Advanced tab, enable the OAuth 2.0 Mutual TLS Certificate Bound Access Tokens Enabled toggle. -
(Optional, to test mTLS Client Authentication) Create another confidential client
client-tls-authwith settings similar to theserviceclient created above. From the Credentials tab, select the X509 Certificate Client Authenticator and fill the Subject DN field so that it matches the Kong client certificate’s, e.g.:CN=JohnDoe, OU=IT. -
(Optional, to test Demonstrating Proof-of-Possession Client Authentication) Create another confidential client
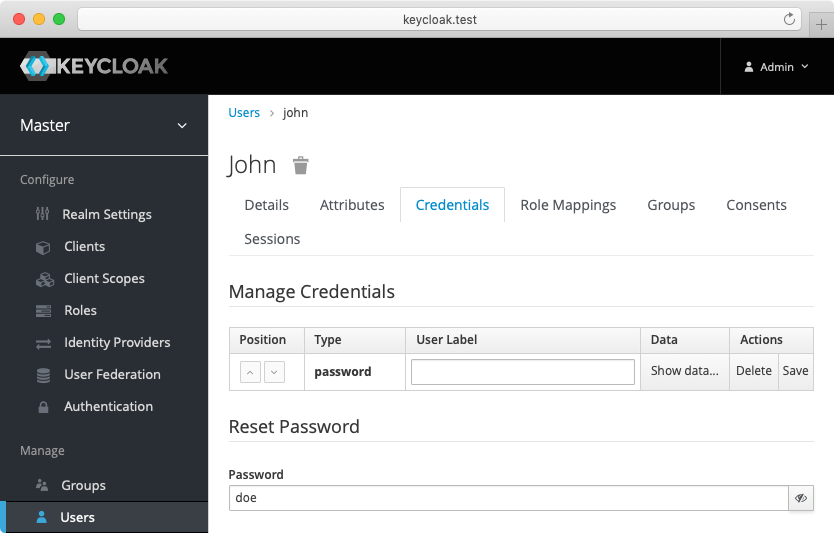
client-dpop-authwith settings similar to theserviceclient created above. From the Advanced tab, enable theOAuth 2.0 DPoP Bound Access Tokens Enabled toggle. - Create a verified user with the name:
johnand the non-temporary password:doethat can be used with the password grant:
Alternatively you can download the exported Keycloak configuration, and use it to configure the Keycloak. Please refer to Keycloak import documentation for more information.
You need to modify Keycloak standalone.xml configuration file, and change the socket binding from:
<socket-binding name="https" port="${jboss.https.port:8443}"/>
to
<socket-binding name="https" port="${jboss.https.port:8440}"/>
The Keycloak default https port conflicts with the default Kong TLS proxy port,
and that can be a problem if both are started on the same host.
Note: The mTLS Client Authentication, along with the proof of possession feature that validates OAuth 2.0 Mutual TLS Certificate Bound Access Tokens, both require configuring Keycloak to validate client certificates with mTLS using the
--https-client-auth=requestoption, and to configure TLS appropriately, including adding the trusted client certificates to the truststore. For more information, refer to the Keycloak documentation.
Configure Kong Gateway
-
Create a service:
curl -i -X POST http://localhost:8001/services \ --data "name=openid-connect" \ --data "url=http://httpbin.org/anything" -
Create a route:
curl -i -X POST http://localhost:8001/services/openid-connect/routes \ --data "name=openid-connect" \ --data "paths[]=/"
Consumer authorization
The following examples are built with simplicity in mind, and are not meant for a production environment. Because
httpbin.orgis the upstream service in these examples, we highly recommended that you do not run these examples with a production identity provider as there is a high chance of leaking information. The examples also use the plain HTTP protocol, which you should never use in production.
Let’s use the following example token payload:
{
"exp": 1622556713,
"aud": "account",
"typ": "Bearer",
"scope": "openid email profile",
"preferred_username": "john",
"given_name": "John",
"family_name": "Doe"
}
Out of these attributes, the preferred_username claim looks promising for consumer mapping.
Configure the OpenID Connect plugin for integration with the ACL plugin. For the purposes of the demo, you can use the password grant.
For the demo, we’re going to set up the following:
- Issuer, client ID, and client auth: settings that connect the plugin to your IdP (in this case, the sample Keycloak app).
- Auth method: password grant (enabled for demo purposes).
- The
preferred_usernameclaim from the example payload.
Test consumer-based authorization
-
Before moving on, make sure the consumer
johndoesn’t exist:curl -i -X DELETE http//localhost:8001/consumers/john -
Now try access the service without a matching consumer:
curl --user john:doe http://localhost:8000You should get an HTTP 403 Forbidden response.
-
Now, add the consumer:
curl -i -X PUT http://localhost:8001/consumers/johnYou should get an HTTP 200 if the consumer creation is successful.
-
Try to access the service again using the same consumer:
curl --user john:doe http://localhost:8000This time, you should get an HTTP 200 response. You should also see that the plugin added
X-Consumer-IdandX-Consumer-Usernameas request headers:{ "headers": { "Authorization": "Bearer <access-token>", "X-Consumer-Id": "<consumer-id>", "X-Consumer-Username": "john" }, "method": "GET" }
It is possible to make consumer mapping optional and non-authorizing by setting the configuration parameter
config.consumer_optional=true.












