This sections gives an overview of a Kong Mesh service mesh. It also covers how to start integrating your services into your mesh.
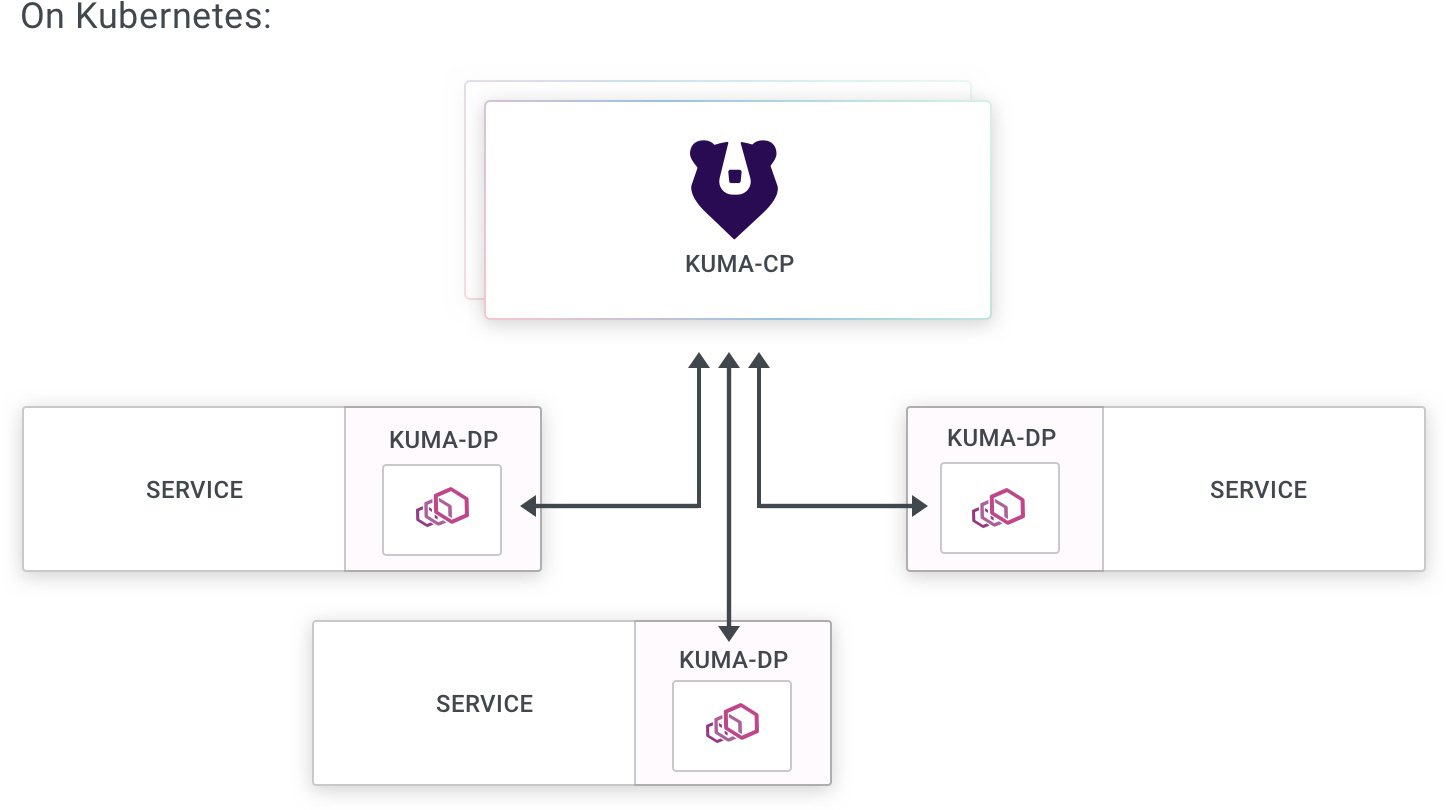
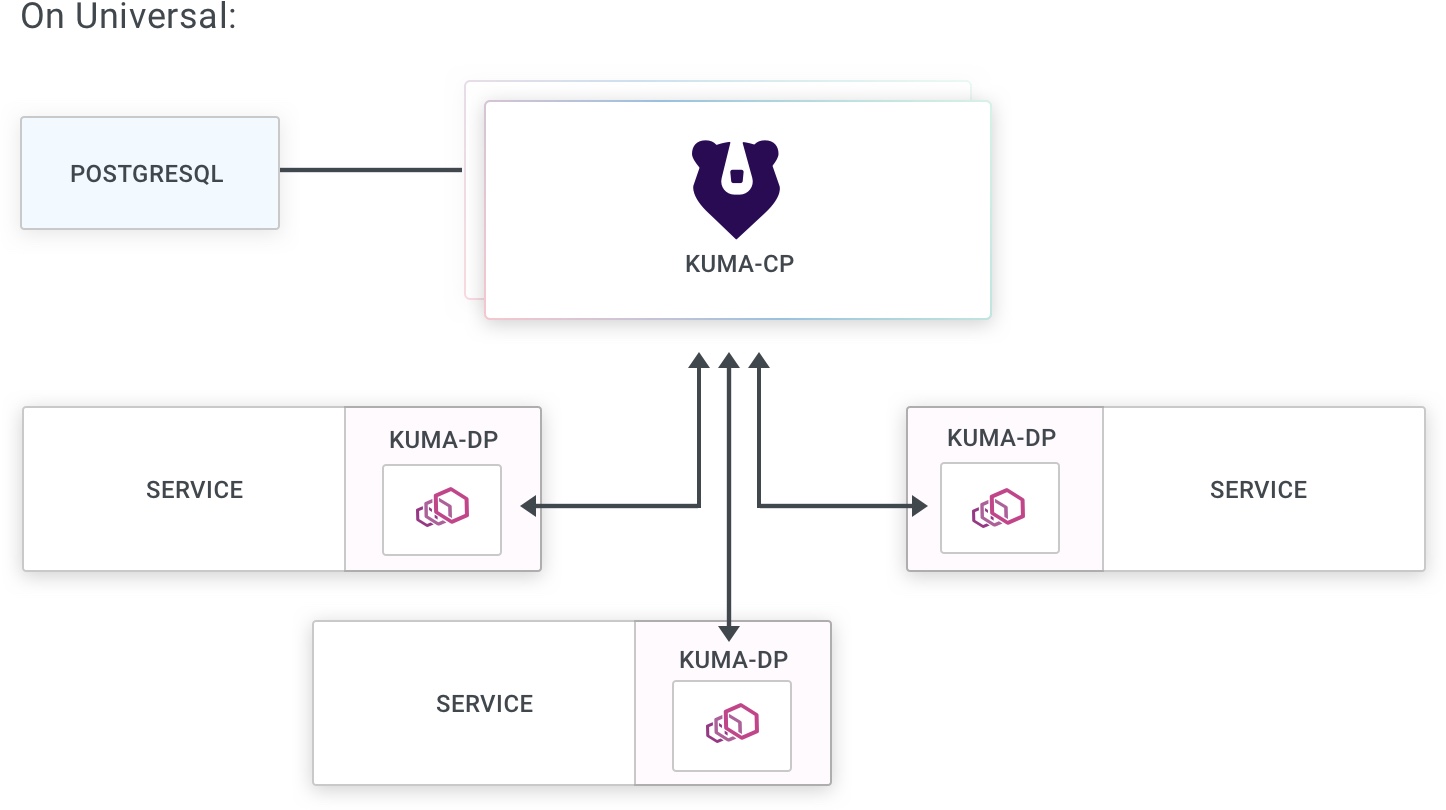
A Kong Mesh mesh consists of two main components:
- The data plane consists of the proxies that run alongside your services. All of your mesh traffic flows through these proxies on its way to its destination. Kong Mesh’s uses Envoy for its data plane proxy.
- The control plane configures the data plane proxies for handling mesh traffic. However, the control plane runs independently of the data plane and does not interact with mesh traffic directly. Kong Mesh users create policies that the Kong Mesh control plane processes to generate configuration for the data plane proxies.
Multi-mesh: one Kong Mesh control plane deployment can control multiple, isolated data planes using the
Meshresource. As compared to one control plane per data plane, this option lowers the complexity and operational cost of supporting multiple meshes.
This is a high level visualization of a Kong Mesh service mesh:
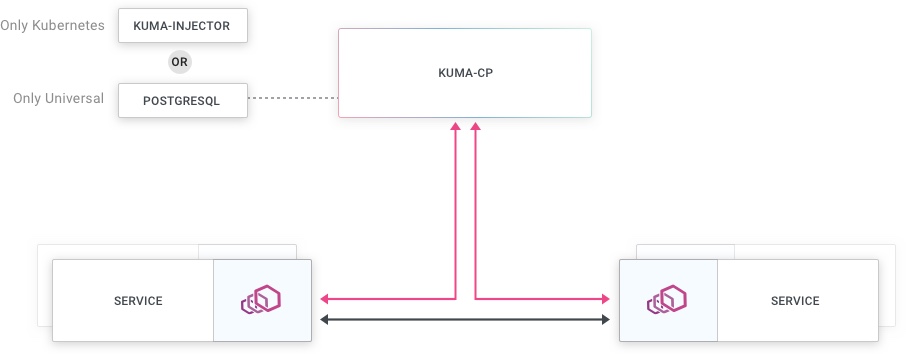
Communication happens between the control and data plane as well as between the services and their data plane proxies:
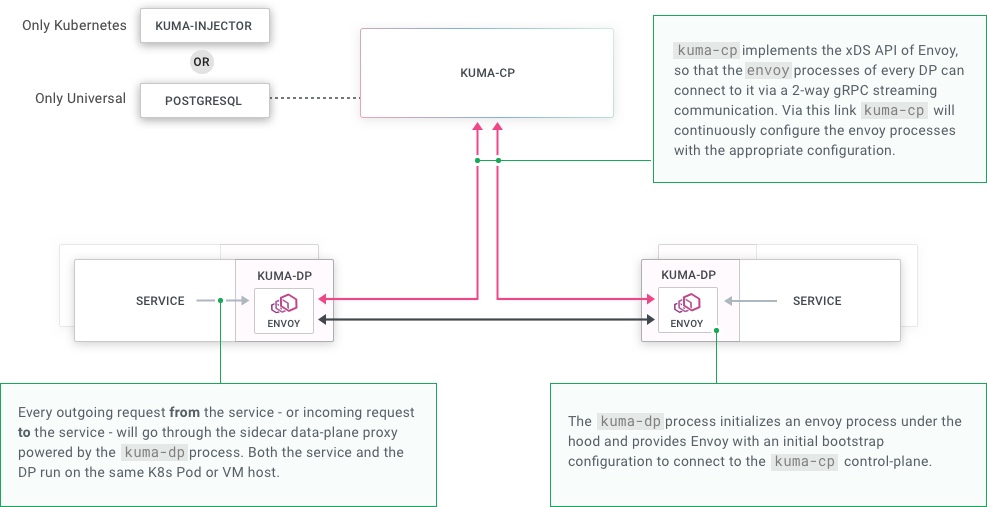
Kong Mesh implements the Envoy xDS APIs so that data plane proxies can retrieve their configuration from the control plane.