Gateway Discovery
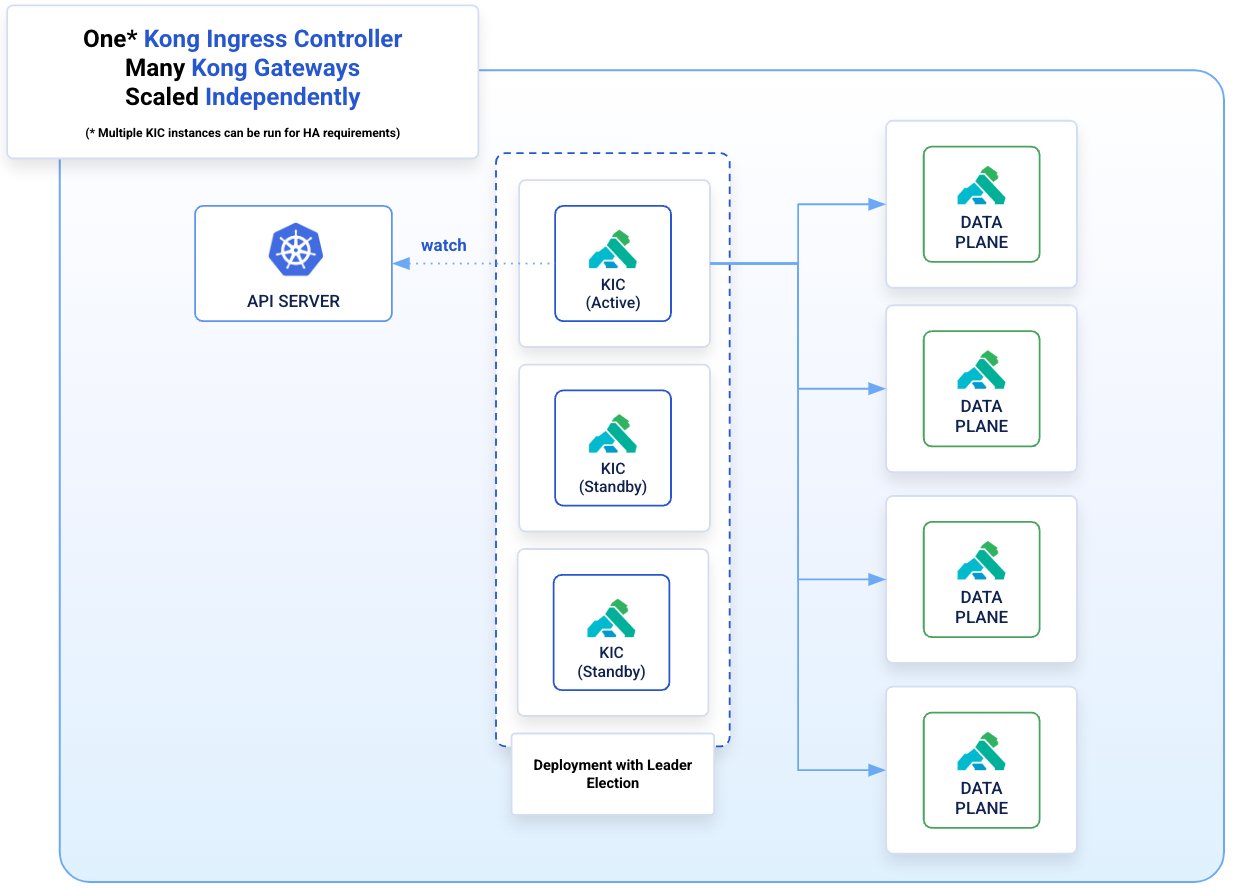
Gateway Discovery is a deployment topology in which Kong Ingress Controller and Kong Gateway are separate deployments in the Kubernetes cluster. Kong Ingress Controller uses Kubernetes service discovery to discover the Kong Gateway Pods.
It allows you to manage many Kong Gateway instances with one Kong Ingress Controller, providing lower resource usage compared to sidecar deployments.
How It Works
You don’t need to configure this manually due to the default value of
gatewayDiscovery.generateAdminApiService=truein the Helm chart. The following information is for educational purposes only.
When Kong Ingress Controller starts running it looks for services that match the name in the --kong-admin-svc flag. This value is controlled by the gatewayDiscovery.adminApiService.namespace and gatewayDiscovery.adminApiService.name values in the Helm chart. Once the service is found, Kong Ingress Controller fetches a list of EndpointSlices containing all Kong Gateway instances.
Kong Ingress Controller proceeds to send configuration to all detected Kong Gateway instances using the POST /config endpoint on each running data plane. Once the data plane has loaded configuration, it is marked as ready and can start proxying traffic.